Suped supports SAML-based single sign-on (SSO) for enterprise organizations. SAML allows your team to log in using your existing identity provider, such as Microsoft Entra, Okta, or Google Workspace.
How it works
- SSO is configured per-organization with a specific email domain.
- Users with a matching email domain are required to log in via your identity provider.
- On first login, users with the configured domain are auto-provisioned. No manual invitation required.
Setting up SAML SSO
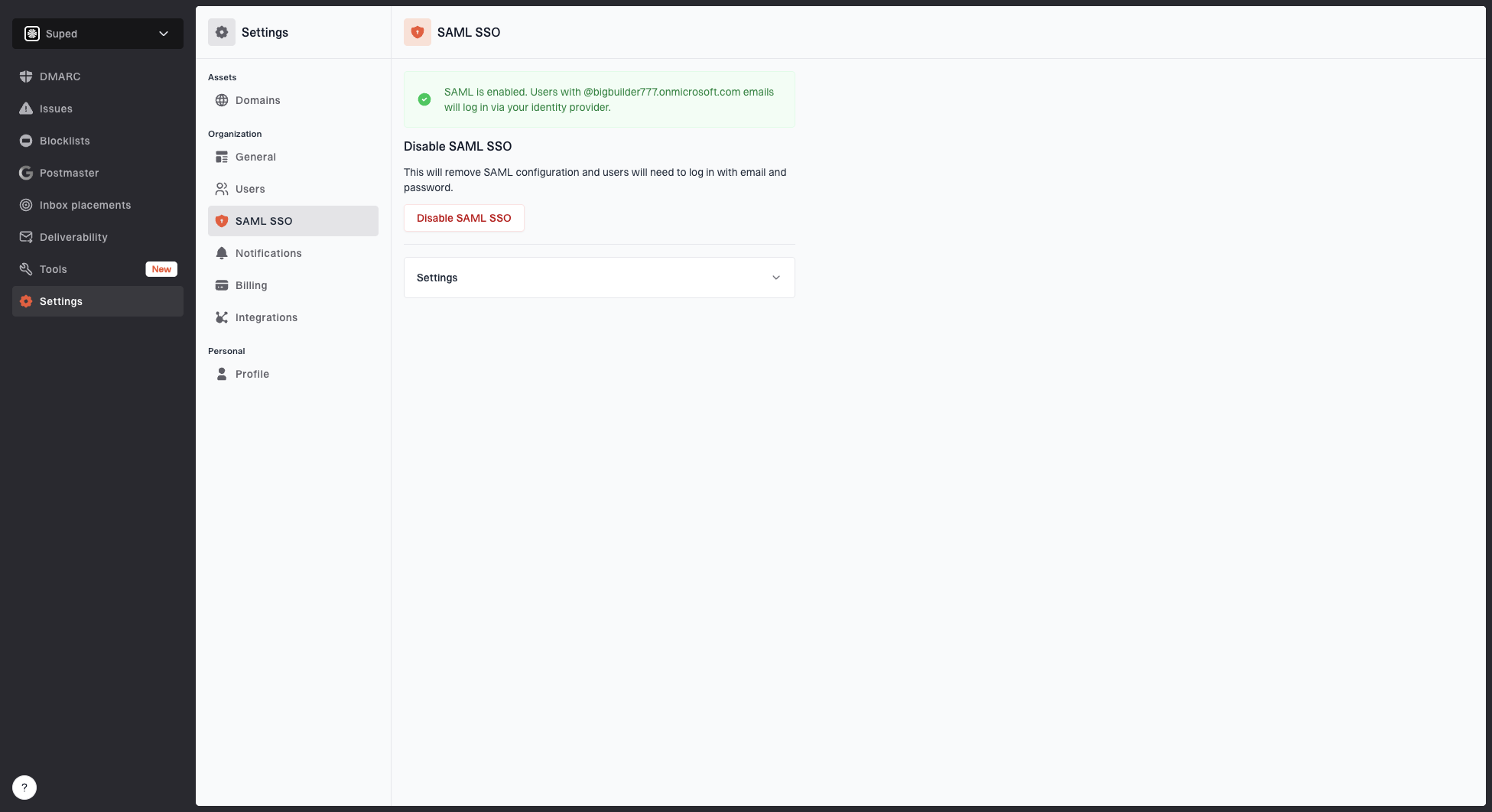
- Go to Settings > SAML SSO.
- Click Download metadata.xml and upload this file to your identity provider when configuring the SAML application.
- Enter your email domain (e.g.
example.com). Users with this email domain will be required to log in via SAML. - Enter your IdP metadata URL. This is the federation metadata XML URL from your identity provider. See the provider notes below for where to find it.
- Verify domain ownership by adding a DNS TXT record at
_suped-verify.yourdomain.comwith the value shown on the page. You can remove this record after saving successfully. - Click Save. Suped will fetch your metadata and verify domain ownership.
Finding your IdP metadata URL
Microsoft Entra (Azure AD)
In the Azure portal, open Enterprise Applications, select your Suped application, then go to Single sign-on. Under SAML Certificates, copy the value of App Federation Metadata Url.
The URL must include an ?appid= query parameter and looks like:
https://login.microsoftonline.com/<tenant-id>/federationmetadata/2007-06/federationmetadata.xml?appid=<application-id>
Do not use the tenant-wide federation metadata URL (the one without ?appid=). It points at the whole tenant instead of your Suped application and SSO will fail at sign-in.
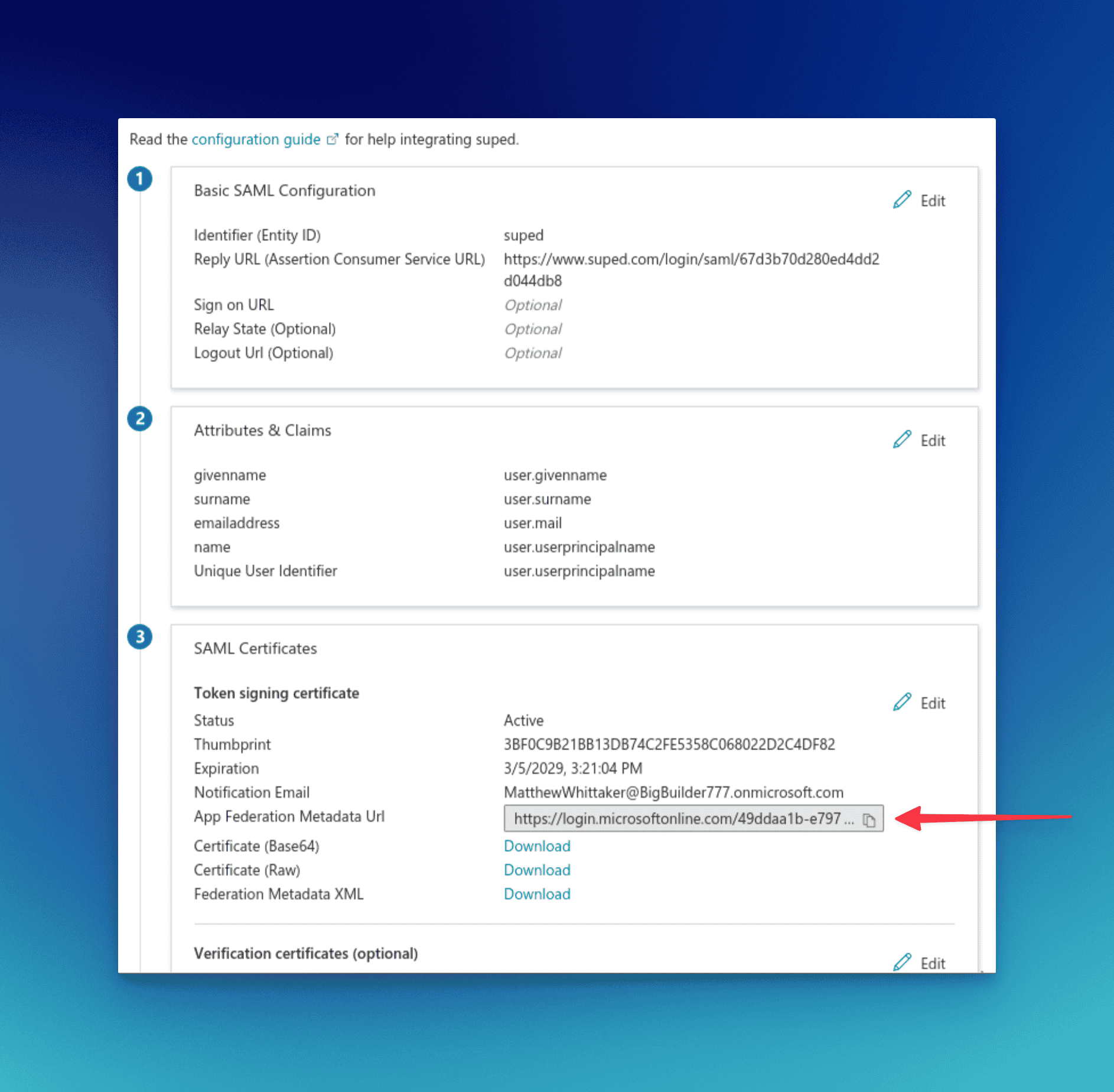
The correct URL is the App Federation Metadata Url field shown above, not the Federation Metadata XML download link below it.
Okta
In the Okta admin console, open your Suped SAML application, go to the Sign On tab, and copy the Metadata URL shown under SAML Signing Certificates.
Google Workspace
Google Workspace does not publish a metadata URL. Configure the SAML app manually using the SSO URL, Entity ID, and certificate from the Google Admin console, or host the IdP metadata XML at a URL you control and paste that URL here.
After setup
Once SAML is enabled, anyone logging in with an email address matching your configured domain will be redirected to your identity provider. New users are automatically provisioned on their first login.
Disabling SAML SSO
To disable SAML, go to Settings > SAML SSO and click Disable SAML SSO. Users will need to log in with email and password after disabling.
